TL;DR: In 2020, a software update accidentally revealed the secret “match scores” and “automation rules” IRCC uses to deny visas. Internal documents reveal a multi-year effort to hide this data through “band-aid” redactions, legal maneuvering, and eventually, rewriting the software to erase the evidence.
For years, applicants denied an Electronic Travel Authorization (eTA) or visa have relied on Global Case Management System (GCMS) notes to understand why. Usually, these notes are cryptic. But in late 2020, a software update—referred to internally as a “system glitch”—accidentally pulled back the curtain on the automated decision-making process.
What followed was a scramble within Immigration, Refugees and Citizenship Canada (IRCC) to hide these “backend rules” from the public, a legal battle with the Information Commissioner, and a strategic pivot to keep the algorithms secret even after a ruling against them.
The “Glitch” of October 2020
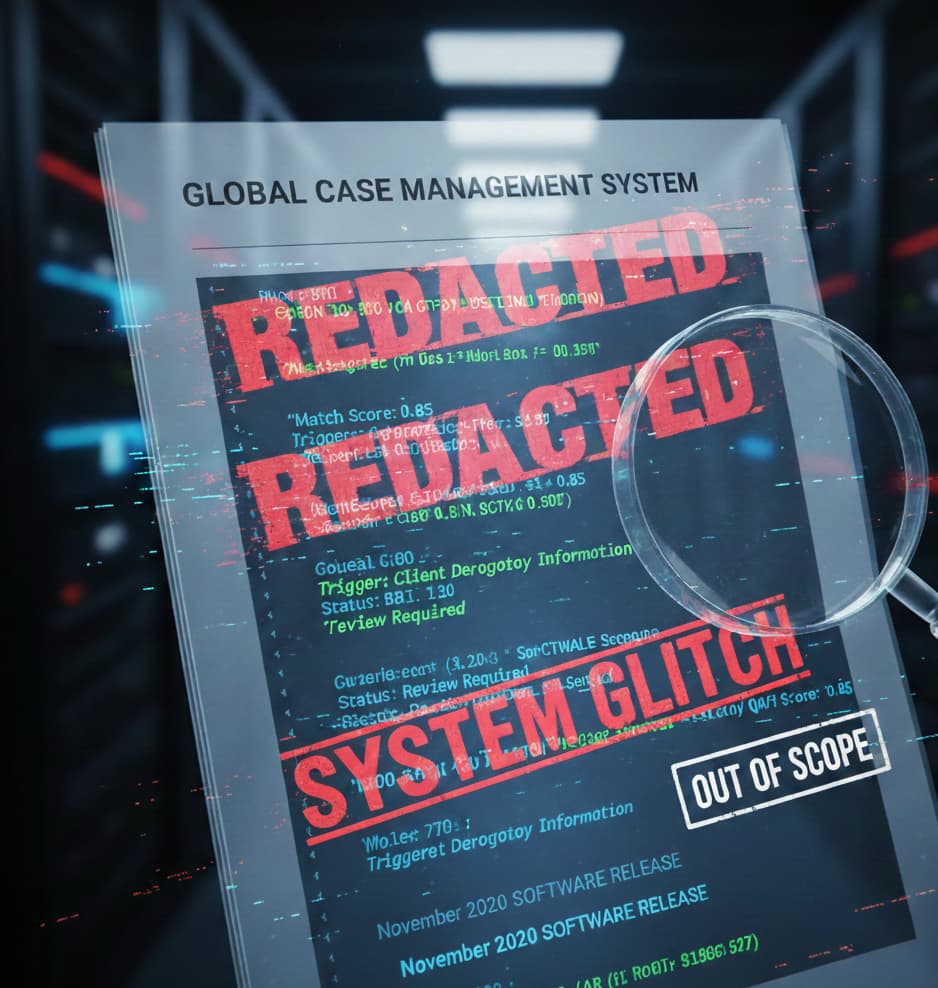
In late 2020, IRCC staff noticed something unusual in the Access to Information (ATIP) reports. A software release caused the “History” section to display granular details about how the computer system assessed files. Instead of just seeing a final decision, applicants could see:
- Match Scores: Specific numbers used to validate identity.
- Trigger Activities: Sub-activities like “Validate CAN Visa” or “Client Derogatory Information.”
- Status Codes: Flags indicating exactly which part of an application triggered a “Review Required” status.
The “Band-Aid” Solution
IRCC officials panicked. Internal correspondence reveals the department feared this detail would provide a “how-to” guide for bad actors to “circumnavigate the system.”
To stop the flow of information, staff were instructed to use a “band-aid solution.” They stamped affected pages as “System Glitch” or “Out of Scope” and withheld them as “Not Relevant.” Applicants were sent generic letters claiming a system error was affecting report generation—a delay tactic while a legal exemption was sought.
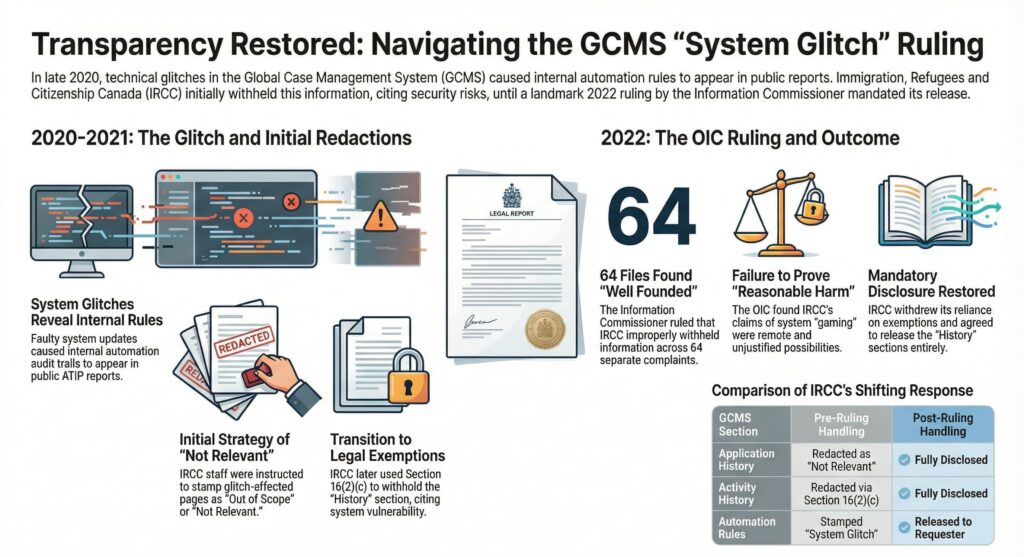
The Legal Battle: OIC Decision 2022-01
The strategy of deeming pages “Not Relevant” failed. Following a complaint, the Office of the Information Commissioner (OIC) investigated.
IRCC argued under Section 16(2)(c) of the Access to Information Act that releasing this data would facilitate crimes by allowing applicants to “game” the system. However, in Decision 2022 OIC 01, the Commissioner rejected this, stating the fear of manipulation was a “mere possibility” and the link to criminal activity was “too remote.”
The Pivot: Changing the Locks
IRCC lost the argument, but they didn’t release the rules. Instead, they changed the legal justification.
Internal directives from December 2021 show managers instructed staff to stop using s.16(2)(c) and instead apply Section 16(1)(c)—an exemption for information “injurious to the enforcement of any law.” By switching labels, IRCC continued to withhold the exact same data the OIC had just ordered them to be transparent about.
The Endgame: Hard-Coding the Secrecy
Realizing that manual redaction was unsustainable, IRCC initiated a technical overhaul. Internal emails reveal a “Change Request” to redesign how GCMS reports are generated.
The goal was to “rebuild” the reporting module so that automation rules would no longer even be included in the “client record” generated for ATIP requests. By modifying the software (specifically Release 26), they aimed to filter out these fields before a human analyst ever saw them.
Where Things Stand Today: The Window Closes
In January 2022, the OIC ruled the complaints well-founded. While the specific complainant received their unredacted files, the victory for the general public was short-lived:
- The Legal Shell Game: If you request GCMS notes today, the logic is still redacted.
- The Technical Erasure: The “glitch” has been “patched.” The window where applicants could see the machinery has been boarded up by rewriting the code to ensure the evidence no longer exists in a printable format.
Why It Matters
While IRCC’s public website offers a polite overview of “identity reconciliation,” they draw a hard line at revealing the logic behind it. As automation expands, the tension between protecting the system and providing procedural fairness grows.
The battle over the 2020 “glitch” proved that when transparency clashes with the convenience of automation, the government will go to extraordinary lengths to keep the black box closed.